Dynamic Quantization-Aware Neural Architecture Search for Real-Time Encrypted Traffic Classification in 5G Networks
DOI:
https://doi.org/10.58564/IJSER.5.1.2026.365Keywords:
Encrypted Traffic Classification, Neural Architecture Search (NAS), Dynamic Quantization, Lightweight Convolutional Neural Networks (CNNs), 5G Edge ComputingAbstract
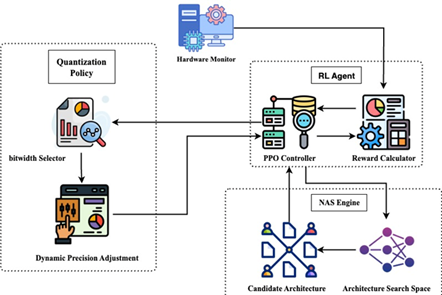
This paper presents a dynamic quantization-aware neural architecture search (NAS) framework for real-time encrypted traffic classification in 5G networks. The framework jointly optimizes model architecture and quantization policies using reinforcement learning with hardware-in-the-loop feedback, addressing both accuracy and efficiency on edge devices. Unlike conventional static methods, the proposed system supports runtime bitwidth switching to adapt precision levels based on fluctuating traffic loads and hardware conditions. Extensive experiments were conducted on ISCX-VPN, USTC-TFC2016, and QUIC-5G datasets. The results show that the proposed approach achieves 94.2% accuracy on ISCX-VPN, 92.7% on USTC, and 89.4% on QUIC-5G, outperforming baseline methods while reducing inference latency by 28–42% and lowering energy consumption by up to 26%. The framework maintains robustness under low-precision constraints, with a mean Quantization Stability Score (QSS) of 0.91, compared to 0.82–0.87 for existing approaches. Hardware-specific optimizations provide additional gains, such as a 2.1 × speedup on Raspberry Pi 4, reduced latency on Jetson Xavier and lower energy consumption on Intel NCS2. The results of Ablation studies affirm that dynamic quantization, hardware feedback, and stability and mechanisms are an absolute necessity, improving accuracy by up to 3.1% and decreasing latency by 31% over sequential optimization. These results prove the efficiency of dynamic quantization-aware NAS to classify encrypted traffic and emphasize its prospects in broader 5G edge AI applications.
References
[1] Z. Cao, G. Xiong, Y. Zhao, Z. Li, and L. Guo, “A survey on encrypted traffic classification,” in Applications and Techniques in Information Security, L. Batten, G. Li, W. Niu, and M. Warren, Eds., Communications in Computer and Information Science, vol. 490. Berlin, Germany: Springer, 2014, pp. 73–81. doi: 10.1007/978-3-662-45670-5_8. DOI: https://doi.org/10.1007/978-3-662-45670-5_8
[2] M. Lotfollahi, M. J. Siavoshani, R. S. Hossein Zade, and M. Saberian, “Deep packet: A novel approach for encrypted traffic classification using deep learning,” arXiv preprint, arXiv:1709.02656, 2018. doi: 10.48550/arXiv.1709.02656. DOI: https://doi.org/10.1007/s00500-019-04030-2
[3] H. Pham, M. Guan, B. Zoph, Q. V. Le, and J. Dean, “Efficient neural architecture search via parameter sharing,” in Proc. 35th Int. Conf. Machine Learning (ICML), J. Dy and A. Krause, Eds., vol. 80. Stockholm, Sweden: PMLR, 2018, pp. 4095–4104. [Online]. Available: http://proceedings.mlr.press/v80/pham18a/pham18a.pdf
[4] H. Liu, K. Simonyan, and Y. Yang, “DARTS: Differentiable architecture search,” arXiv preprint, arXiv:1806.09055, 2018. [Online]. Available: https://arxiv.org/pdf/1806.09055
[5] B. Jacob, S. Kligys, B. Chen, M. Zhu, et al., “Quantization and training of neural networks for efficient integer-arithmetic-only inference,” in Proc. IEEE Conf. Computer Vision and Pattern Recognition (CVPR), 2018, pp. 2704–2713. [Online]. Available: DOI: https://doi.org/10.1109/CVPR.2018.00286
[6] B. Wang, J. Wu, X. Liang, Y. Liu, H. Li, and L. Lin, “HAQ: Hardware-aware automated quantization with mixed precision,” arXiv preprint, arXiv:1805.06085, 2018. doi: 10.48550/arXiv.1805.06085. DOI: https://doi.org/10.1109/CVPR.2019.00881
[7] J. Cheng, R. He, Y. E, Y. Wu, J. You, and T. Li, “Real-time encrypted traffic classification via lightweight neural networks,” in Proc. 2020 IEEE Global Communications Conference (GLOBECOM), Taipei, Taiwan, 2020, pp. 1–6. doi: 10.1109/GLOBECOM42002.2020.9322309.
[8] A. G. Howard, M. Zhu, B. Chen, D. Kalenichenko, W. Wang, T. Weyand, M. Andreetto, and H. Adam, “MobileNets: Efficient convolutional neural networks for mobile vision applications,” arXiv preprint, arXiv:1704.04861, 2017. doi: 10.48550/arXiv.1704.04861
[9] X. Zhang, X. Zhou, M. Lin and J. Sun, "ShuffleNet: An Extremely Efficient Convolutional Neural Network for Mobile Devices," 2018 IEEE/CVF Conference on Computer Vision and Pattern Recognition, Salt Lake City, UT, USA, 2018, pp. 6848-6856, doi: 10.1109/CVPR.2018.00716. DOI: https://doi.org/10.1109/CVPR.2018.00716
[10] H. Cai, L. Zhu, and S. Han, “ProxylessNAS: Direct neural architecture search on target task and hardware,” arXiv preprint, arXiv:1812.00332, 2018. doi: 10.48550/arXiv.1812.00332.
[11] B. Wu, X. Dai, P. Zhang, Y. Wang, F. Sun, Y. Wu, Y. Tian, P. Vajda, Y. Jia, and K. Keutzer, “FBNet: Hardware aware efficient ConvNet design via differentiable neural architecture search,” arXiv preprint, arXiv:1812.03443, 2019. doi: 10.48550/arXiv.1812.03443 DOI: https://doi.org/10.1109/CVPR.2019.01099
[12] R. T. Elmaghraby, N. M. Abdel Aziem, M. A. Sobh, and A. M. Bahaa Eldin, “Encrypted network traffic classification based on machine learning,” Ain Shams Eng. J., vol. 15, no. 2, p. 102361, 2023. doi: 10.1016/j.asej.2023.102361. DOI: https://doi.org/10.1016/j.asej.2023.102361
[13] S. Rezaei and X. Liu, "Deep Learning for Encrypted Traffic Classification: An Overview," in IEEE Communications Magazine, vol. 57, no. 5, pp. 76-81, May 2019, doi: 10.1109/MCOM.2019.1800819. DOI: https://doi.org/10.1109/MCOM.2019.1800819
[14] J. Cheng, R. He, E. Yuepeng, Y. Wu, J. You and T. Li, "Real-Time Encrypted Traffic Classification via Lightweight Neural Networks," GLOBECOM 2020 - 2020 IEEE Global Communications Conference, Taipei, Taiwan, 2020, pp. 1-6, doi: 10.1109/GLOBECOM42002.2020.9322309. DOI: https://doi.org/10.1109/GLOBECOM42002.2020.9322309
[15] S. Dhanasekaran, T. Thamaraimanalan, P. Vivek Karthick, and D. Silambarasan, “A lightweight CNN with LSTM malware detection architecture for 5G and IoT networks,” IETE J. Res., vol. 70, no. 9, pp. 7100–7111, 2024. doi: 10.1080/03772063.2024.2352151. DOI: https://doi.org/10.1080/03772063.2024.2352151
[16] C. H. Lin, T. Y. Chen, H. Y. Chen, and Y. K. Chan, “Efficient and lightweight convolutional neural network architecture search methods for object classification,” Pattern Recognit., p. 110752, 2024. doi: 10.1016/j.patcog.2024.110752. DOI: https://doi.org/10.1016/j.patcog.2024.110752
[17] B. Zoph and Q. V. Le, “Neural architecture search with reinforcement learning,” arXiv preprint, arXiv:1611.01578, 2016. [Online]. Available: https://arxiv.org/pdf/1611.01578
[18] Z. Dong, Z. Yao, A. Gholami, M. W. Mahoney, and K. Keutzer, “HAWQ: Hessian AWare quantization of neural networks with mixed precision,” arXiv preprint, arXiv:1905.03696, 2019. doi: 10.48550/arXiv.1905.03696. DOI: https://doi.org/10.1109/ICCV.2019.00038
[19] M. Shen et al., "Once Quantization-Aware Training: High Performance Extremely Low-bit Architecture Search," 2021 IEEE/CVF International Conference on Computer Vision (ICCV), Montreal, QC, Canada, 2021, pp. 5320-5329, doi: 10.1109/ICCV48922.2021.00529. DOI: https://doi.org/10.1109/ICCV48922.2021.00529
[20] T. Wang et al., "APQ: Joint Search for Network Architecture, Pruning and Quantization Policy," 2020 IEEE/CVF Conference on Computer Vision and Pattern Recognition (CVPR), Seattle, WA, USA, 2020, pp. 2075-2084, doi: 10.1109/CVPR42600.2020.00215. DOI: https://doi.org/10.1109/CVPR42600.2020.00215
[21] K. Kim, S. Choi, H. Kwon, H. Kim, Z. Liu, and H. Seo, “PAGE—Practical AES-GCM encryption for low-end microcontrollers,” Appl. Sci., vol. 10, no. 9, p. 3131, 2020. doi: 10.3390/app10093131. DOI: https://doi.org/10.3390/app10093131
[22] E. Dahlman, S. Parkvall, and J. Sköld, 5G NR: The Next Generation Wireless Access Technology, 3rd ed. Oxford, UK: Academic Press, 2020. [Online]. Available: https://ie.u-ryukyu.ac.jp/~wada/system18/5G_Book.pdf
[23] E. Mahdavi, A. Fanian, and H. Hassannejad, “Encrypted traffic classification using statistical features,” Int. J. Inf. Secur., vol. 10, no. 1, pp. 29–43, 2018.
[24] G. Sopidis, M. Haslgrübler, and A. Ferscha, “Counting activities using weakly labeled raw acceleration data: A variable length sequence approach with deep learning to maintain event duration flexibility,” Sensors, vol. 23, no. 11, p. 5057, 2023. doi: 10.3390/s23115057. DOI: https://doi.org/10.3390/s23115057
[25] J. Schulman, F. Wolski, P. Dhariwal, A. Radford, and O. Klimov, “Proximal policy optimization algorithms,” arXiv preprint, arXiv:1707.06347, 2017. doi: 10.48550/arXiv.1707.06347.
[26] H. Benmeziane, K. El Maghraoui, H. Ouarnoughi, S. Niar, M. Wistuba, and N. Wang, “Hardware aware neural architecture search: survey and taxonomy,” in Proc. Thirtieth Int. Joint Conf. Artificial Intelligence (IJCAI ’21), Z. H. Zhou, Ed., Montreal, Canada, 2021, pp. 4322–4329. doi: 10.24963/ijcai.2021/592. DOI: https://doi.org/10.24963/ijcai.2021/592
[27] S. K. Esser, J. L. McKinstry, D. Bablani, R. Appuswamy, and D. S. Modha, “Learned step size quantization,” arXiv preprint, arXiv:1902.08153, 2019. doi: 10.48550/arXiv.1902.08153.
[28] Y. Zhou and K. Yang, "Exploring TensorRT to Improve Real-Time Inference for Deep Learning," 2022 IEEE 24th Int Conf on High Performance Computing & Communications; 8th Int Conf on Data Science & Systems; 20th Int Conf on Smart City; 8th Int Conf on Dependability in Sensor, Cloud & Big Data Systems & Application (HPCC/DSS/SmartCity/DependSys), Hainan, China, 2022, pp. 2011-2018, doi: 10.1109/HPCC-DSS-SmartCity-DependSys57074.2022.00299. DOI: https://doi.org/10.1109/HPCC-DSS-SmartCity-DependSys57074.2022.00299
[29] U. Kulkarni, S. M. Meena, S. V. Gurlahosur, and G. Bhogar, “Quantization friendly MobileNet (QF MobileNet) architecture for vision based applications on embedded platforms,” Neural Netw., vol. 136, pp. 28–39, Apr. 2021. doi: 10.1016/j.neunet.2020.12.022. DOI: https://doi.org/10.1016/j.neunet.2020.12.022
[30] C. Wang, W. Zhang, H. Hao, and H. Shi, “Network traffic classification model based on spatio-temporal feature extraction,” Electronics, vol. 13, no. 7, p. 1236, 2024. doi: 10.3390/electronics13071236. DOI: https://doi.org/10.3390/electronics13071236
[31] H. Huang, X. Zhang, Y. Lu, Z. Li, and S. Zhou, “BSTFNet: An encrypted malicious traffic classification method integrating global semantic and spatiotemporal features,” Comput. Mater. Contin., vol. 78, no. 3, pp. 3929–3951, 2024. doi: 10.32604/cmc.2024.047918. DOI: https://doi.org/10.32604/cmc.2024.047918
[32] S. Almuhammadi, A. Alnajim, and M. Ayub, “QUIC network traffic classification using ensemble machine learning techniques,” Appl. Sci., vol. 13, no. 8, p. 4725, 2023. doi: 10.3390/app13084725. DOI: https://doi.org/10.3390/app13084725
[33] P. Velan, M. Čermák, P. Čeleda, and M. Drašar, “A survey of methods for encrypted traffic classification and analysis,” Int. J. Network Manage., vol. 25, no. 5, pp. 355–374, 2015. doi: 10.1002/nem.1901. DOI: https://doi.org/10.1002/nem.1901
[34] M. Burhanuddin, “Efficient Hardware Acceleration Techniques for Deep Learning on Edge Devices: A Comprehensive Performance Analysis”, KHWARIZMIA, vol. 2023, pp. 103–112, Aug. 2023, doi: 10.70470/KHWARIZMIA/2023/010. DOI: https://doi.org/10.70470/KHWARIZMIA/2023/010
[35] A. Howard et al., "Searching for MobileNetV3," 2019 IEEE/CVF International Conference on Computer Vision (ICCV), Seoul, Korea (South), 2019, pp. 1314-1324, doi: 10.1109/ICCV.2019.00140. DOI: https://doi.org/10.1109/ICCV.2019.00140
[36] Q. Lou, F. Guo, L. Liu, M. Kim, and L. Jiang, “AutoQ: automated kernel wise neural network quantization,” arXiv preprint, arXiv:1902.05690, 2019. doi: 10.48550/arXiv.1902.05690.
[37] M. Perrin, W. Guicquero, B. Paille and G. Sicard, "Hardware-Aware Bayesian Neural Architecture Search of Quantized CNNs," in IEEE Embedded Systems Letters, vol. 17, no. 1, pp. 42-45, Feb. 2025, doi: 10.1109/LES.2024.3434379. DOI: https://doi.org/10.1109/LES.2024.3434379
[38] N. Malekghaini et al., "AutoML4ETC: Automated Neural Architecture Search for Real-World Encrypted Traffic Classification," in IEEE Transactions on Network and Service Management, vol. 21, no. 3, pp. 2715-2730, June 2024, doi: 10.1109/TNSM.2023.3324936. DOI: https://doi.org/10.1109/TNSM.2023.3324936
[39] S. Hooker, N. Moorosi, G. Clark, S. Bengio, and E. Denton, “Characterising bias in compressed models,” arXiv preprint, arXiv:2010.03058, 2020. doi: 10.48550/arXiv.2010.03058.
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Abdullah Ghanim Jaber, Abeer Ahmed Ali, Ali A. Mahmood, Mohammed Jamal Salim, Ghaith Jaafar Mohammed, Khairul Akram Zainol Ariffin

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Deprecated: json_decode(): Passing null to parameter #1 ($json) of type string is deprecated in /var/www/vhosts/ijser.aliraqia.edu.iq/httpdocs/plugins/generic/citations/CitationsPlugin.inc.php on line 49