Efficient Hybrid Machine Learning and Feature Selection Approach for IoMT Attack Detection and Healthcare Security Enhancement
DOI:
https://doi.org/10.58564/IJSER.5.1.2026.361Keywords:
Internet of Medical Things (IoMT), Intrusion Detection System (IDS), Particle Swarm Optimization (PSO), Machine Learning (ML), Cybersecurity, Smart Healthcare, Attack DetectionAbstract
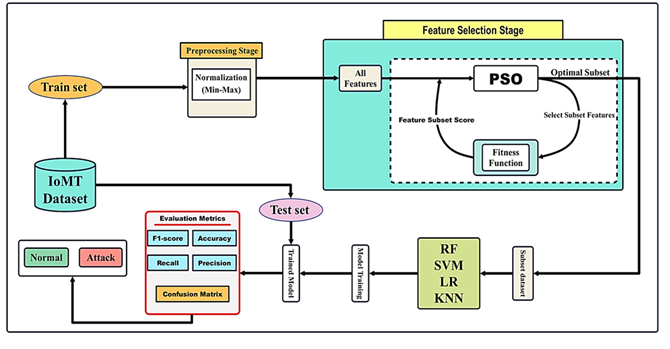
The increasing interconnectivity of healthcare devices through the Internet of Medical Things (IoMT) has improved patient monitoring and treatment, but also exposed these systems to malicious cyberattacks that threaten both patient safety and data integrity. Existing machine learning (ML)-based approaches have attempted to detect such attacks, but most rely on all dataset features, including irrelevant and redundant ones, which increases computational cost and reduces detection accuracy. Feature selection techniques such as Particle Swarm Optimization (PSO) have been used to address this challenge, yet their default fitness functions fail to select the most suitable features for each classifier, often leading to suboptimal results. To overcome these limitations, this study introduces a novel fitness function integrated with PSO and ML classifiers to identify the most relevant features for accurate attack detection in IoMT devices. The proposed framework was evaluated using the NSL-KDD dataset (41 features) with RF, KNN, SVM, and LR classifiers. The number of correctly predicted labels for the optimal feature subsets was 99.35% for RF, 99.02% for KNN, 98.20% for SVM, and 97.61% for LR, whereas the baseline accuracies for the cases with all the features were 95.41%, 94.76%, 92.86%, and 89.55%, respectively. Moreover, the execution times decreased by almost one-third, showing the efficiency of the method. The report indicates validation of the PSO-based fitness function developed for lightweight-accuracy attacks detection in IoMT devices, thus proving to be efficient and cost-conducive, readily deployable in medical organizations as well as smart home environments, thereby safeguarding future-proof healthcare infrastructures against dynamically evolving threats.
References
[1] D. V. Dimitrov, “Medical internet of things and big data in healthcare,” Healthcare informatics research, vol. 22, no. 3, pp. 156–163, 2016. DOI: https://doi.org/10.4258/hir.2016.22.3.156
[2] M. H. Mohammed, M. N. Kadhim, D. Al-Shammary, and A. Ibaida, “Novel Voice Signal Segmentation Based on Clark Distance to Improve Intelligent Parkinson Disease Detection,” Journal of Voice, 2025. DOI: https://doi.org/10.1016/j.jvoice.2025.04.030
[3] P. Manickam et al., “Artificial intelligence (AI) and internet of medical things (IoMT) assisted biomedical systems for intelligent healthcare,” Biosensors, vol. 12, no. 8, p. 562, 2022. DOI: https://doi.org/10.3390/bios12080562
[4] A. A. Laklook, S. Khosroabadi, and A. H. Al-fatlawi, “A Special Design of Job Dropout Faces Detection and Recognition System (JDFDRs),” presented at the 2021 International Conference on Advanced Computer Applications (ACA), IEEE, 2021, pp. 138–143. DOI: https://doi.org/10.1109/ACA52198.2021.9626784
[5] M. N. Kadhim, A. H. Mutlag, D. A. Hammood, and N. B. H. Ismail, “Identification of Vehicle Logos in Deep Learning: A Comprehensive Survey,” Journal of Techniques, vol. 7, no. 1, pp. 37–47, 2025. DOI: https://doi.org/10.51173/jt.v7i1.2099
[6] S. S. Baawi, M. N. Kadhim, and D. Al-Shammary, “Efficient feature selection based on Gower distance for breast cancer diagnosis,” Journal of Electronic Science and Technology, vol. 23, no. 2, p. 100315, 2025. DOI: https://doi.org/10.1016/j.jnlest.2025.100315
[7] S. M. Abdulkhudhur, S. M. Abboud, A. H. Najim, M. N. Kadhim, and A. A. Ahmed, “A Hybrid Deep Belief Cascade-Neuro Fuzzy Approach for Real-Time Health Anomaly Detection in 5G-Enabled IoT Medical Networks.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 5, 2025. DOI: https://doi.org/10.22266/ijies2025.0630.12
[8] A. R. Hamad, S. M. Baraa Alsabti, A. H. Najim, and M. N. Kadhim, “A Hybrid Feature Selection and Machine Learning Approach for Parkinson’s Disease Detection from Voice Signals in IoT-Enabled 6G Networks.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 5, 2025. DOI: https://doi.org/10.22266/ijies2025.0630.04
[9] Z. H. Hashim Albohayah, S. B. Abed, A. J. Mahdi, M. N. Kadhim, and A. H. Najim, “Ch-PSO: A Novel Embedded Method based on PSO and Chebyshev Distance for Enhanced Epileptic Seizure Classification Using EEG Brain Signals.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 5, 2025. DOI: https://doi.org/10.22266/ijies2025.0630.37
[10] S. L. Alzamili, S. S. Baawi, M. N. Kadhim, D. Al-Shammary, and A. Ibaida, “Efficient feature selection based on Ruzicka similarity for EEG diagnosis,” International Journal of Information Technology, pp. 1–15, 2025. DOI: https://doi.org/10.1007/s41870-025-02572-3
[11] C. Avula and S. Bachala, “A Deep Feature Ensemble Framework for Intrusion Detection in Internet of Medical Things,” Engineering, Technology & Applied Science Research, vol. 15, no. 5, pp. 26783–26791, 2025. DOI: https://doi.org/10.48084/etasr.12242
[12] A. Salehpour, M. Norouzi, M. A. Balafar, and K. SamadZamini, “A cloud‐based hybrid intrusion detection framework using XGBoost and ADASYN‐Augmented random forest for IoMT,” IET Communications, vol. 18, no. 19, pp. 1371–1390, 2024. DOI: https://doi.org/10.1049/cmu2.12833
[13] S. Farhan, J. Mubashir, Y. U. Haq, T. Mahmood, and A. Rehman, “Enhancing network security: an intrusion detection system using residual network-based convolutional neural network,” Cluster Computing, vol. 28, no. 4, p. 251, 2025. DOI: https://doi.org/10.1007/s10586-025-05156-9
[14] H. Goumidi and S. Pierre, “Real-Time Anomaly Detection in IoMT Networks Using Stacking model and a Healthcare-Specific Dataset,” IEEE Access, 2025. DOI: https://doi.org/10.1109/ACCESS.2025.3563158
[15] A. Khan, M. Rizwan, O. Bagdasar, A. Alabdulatif, S. Alamro, and A. Alnajim, “Deep Learning-Driven Anomaly Detection for IoMT-Based Smart Healthcare Systems.,” CMES-Computer Modeling in Engineering & Sciences, vol. 141, no. 3, 2024. DOI: https://doi.org/10.32604/cmes.2024.054380
[16] M. A. Umar, Z. Chen, K. Shuaib, and Y. Liu, “Effects of feature selection and normalization on network intrusion detection,” Data Science and Management, vol. 8, no. 1, pp. 23–39, 2025. DOI: https://doi.org/10.1016/j.dsm.2024.08.001
[17] Z. Xia, S. He, C. Liu, Y. Liu, X. Yang, and H. Bu, “PSO-GA Hyperparameter Optimized ResNet-BiGRU Based Intrusion Detection Method,” IEEE Access, 2024. DOI: https://doi.org/10.1109/ACCESS.2024.3464529
[18] S. Moualla, K. Khorzom, and A. Jafar, “Improving the Performance of Machine Learning‐Based Network Intrusion Detection Systems on the UNSW‐NB15 Dataset,” Computational Intelligence and Neuroscience, vol. 2021, no. 1, p. 5557577, 2021. DOI: https://doi.org/10.1155/2021/5557577
[19] M. N. Kadhim, A. H. Mutlag, and D. A. Hammood, “Multi-models Based on Yolov8 for Identification of Vehicle Type and License Plate Recognition,” presented at the National Conference on New Trends in Information and Communications Technology Applications, Springer, 2023, pp. 118–135. DOI: https://doi.org/10.1007/978-3-031-62814-6_9
[20] S. S. Mahmood, M. A. Hasan, A. Al-bosham, A. H. Al-Fatlawi, M. S. Abd Al-Ameer, and H. Najm, “Efficient Emotional State Classification based on Bayesian Quantile Regression and PSO Using EEG Brain Signal.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 6, 2025. DOI: https://doi.org/10.22266/ijies2025.0731.14
[21] A. T. Albu-Salih, M. Y. Jumaah, A. H. Al-Fatlawi, and H. Najm, “Efficient Hybrid Feature Engineering and Supervised Learning Approach for Network Traffic Classification in Intrusion Detection Systems.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 6, 2025. DOI: https://doi.org/10.22266/ijies2025.0731.15
[22] M. H. Mohammed, M. N. Kadhim, D. Al-Shammary, and A. Ibaida, “EEG-Based Emotion Detection Using Roberts Similarity and PSO Feature Selection,” IEEE Access, 2025.
[23] A. L. Albukhnefis, A. A. Sakran, A. S. Mahe, M. I. Mousa, and A. M. Mahdi, “Hybrid Intrusion Detection Systems Based Mean-Variance Mapping Optimization Algorithm and Random Search.,” International Journal of Intelligent Engineering & Systems, vol. 16, no. 5, 2023. DOI: https://doi.org/10.22266/ijies2023.1031.47
[24] M. Sadiq, M. N. Kadhim, D. Al-Shammary, and M. Milanova, “Novel EEG feature selection based on hellinger distance for epileptic seizure detection,” Smart Health, vol. 35, p. 100536, 2025. DOI: https://doi.org/10.1016/j.smhl.2024.100536
[25] R. Malik, R. M. Alsharfa, B. K. Mohammed, A. H. Al-Fatlawi, M. S. Abd Al-Ameer, and H. Najm, “A Novel Taneja Distance-based Classifier with PSO-Optimized Feature Selection for Efficient 5G Network Slicing.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 6, 2025. DOI: https://doi.org/10.22266/ijies2025.0731.40
[26] M. N. Kadhim, D. Al-Shammary, and F. Sufi, “A novel voice classification based on Gower distance for Parkinson disease detection,” International Journal of Medical Informatics, vol. 191, p. 105583, 2024. DOI: https://doi.org/10.1016/j.ijmedinf.2024.105583
[27] H. H. Al-Kazzaz, M. J. Hazar, A. Naser, S. A. Razzaq, A. H. Al-Fatlawi, and S. A. Fadhil, “A Hybrid TD-PSO Feature Selection Approach for Accurate Arrhythmia Classification based on ECG Heart Signals.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 7, 2025. DOI: https://doi.org/10.22266/ijies2025.0831.13
[28] M. N. Kadhim, D. Al-Shammary, A. M. Mahdi, and A. Ibaida, “Feature selection based on Mahalanobis distance for early Parkinson disease classification,” Computer Methods and Programs in Biomedicine Update, vol. 7, p. 100177, 2025. DOI: https://doi.org/10.1016/j.cmpbup.2025.100177
[29] M. Sadiq, M. N. Kadhim, D. Al-Shammary, and M. Milanova, “Novel EEG classification based on hellinger distance for seizure epilepsy detection,” IEEE Access, 2024. DOI: https://doi.org/10.1109/ACCESS.2024.3450449
[30] W. H. M. Kurdi, H. A. Rassool, and A. H. Al-fatlawi, “Evaluation patterns and algorithm for cancer identifications using dynamic clustering,” Periodicals of Engineering and Natural Sciences (PEN), vol. 9, no. 2, pp. 462–470, 2021. DOI: https://doi.org/10.21533/pen.v9.i2.755
[31] M. N. Kadhim, A. H. Mutlag, and D. A. Hammood, “Vehicle detection and classification from images/videos using deep learning architectures: A survey,” presented at the AIP Conference Proceedings, AIP Publishing LLC, 2024, p. 020034. DOI: https://doi.org/10.1063/5.0236211
[32] D. Al-Shammary, M. N. Kadhim, A. M. Mahdi, A. Ibaida, and K. Ahmed, “Efficient ECG classification based on Chi-square distance for arrhythmia detection,” Journal of Electronic Science and Technology, vol. 22, no. 2, p. 100249, 2024. DOI: https://doi.org/10.1016/j.jnlest.2024.100249
[33] S. L. Kailan, W. H. Madhloom Kurdi, A. H. Najim, and M. N. Kadhim, “Efficient ECG Classification Based on Machine Learning and Feature Selection Algorithm for IoT-5G Enabled Health Monitoring Systems.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 1, 2025. DOI: https://doi.org/10.22266/ijies2025.0229.86
[34] M. P. Raghunath et al., “PCA and PSO based optimized support vector machine for efficient intrusion detection in internet of things,” Measurement: Sensors, vol. 37, p. 101806, 2025. DOI: https://doi.org/10.1016/j.measen.2024.101806
[35] W. H. Madhloom Kurdi, I. A. Alzuabidi, A. H. Najim, M. N. Kadhim, and A. A. Ahmed, “Efficient Two-Stage Intrusion Detection System Based on Hybrid Feature Selection Techniques and Machine Learning Classifiers.,” International Journal of Intelligent Engineering & Systems, vol. 18, no. 3, 2025. DOI: https://doi.org/10.22266/ijies2025.0430.16
[36] N. Dash, S. Chakravarty, A. K. Rath, N. C. Giri, K. M. AboRas, and N. Gowtham, “An optimized LSTM-based deep learning model for anomaly network intrusion detection,” Scientific Reports, vol. 15, no. 1, p. 1554, 2025. DOI: https://doi.org/10.1038/s41598-025-85248-z
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Mustafa Hasan Merza

This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License.
Deprecated: json_decode(): Passing null to parameter #1 ($json) of type string is deprecated in /var/www/vhosts/ijser.aliraqia.edu.iq/httpdocs/plugins/generic/citations/CitationsPlugin.inc.php on line 49